Table of Contents
In September 2023, MGM Resorts International, one of the largest casino and hospitality operators in the world fell victim to a highly disruptive cyberattack that brought hotel operations, slot machines, digital room keys and payment systems to a standstill.
What makes this incident particularly notable from a security perspective is not just the scale of the impact, but the simplicity of the initial access vector a social engineering call to the IT helpdesk.
Who Was Behind the Attack?
The attack has been attributed to a threat group known as Scattered Spider a financially motivated collective linked to English-speaking operators some of whom are believed to be based in the United States and the United Kingdom.
How Did They Get In?
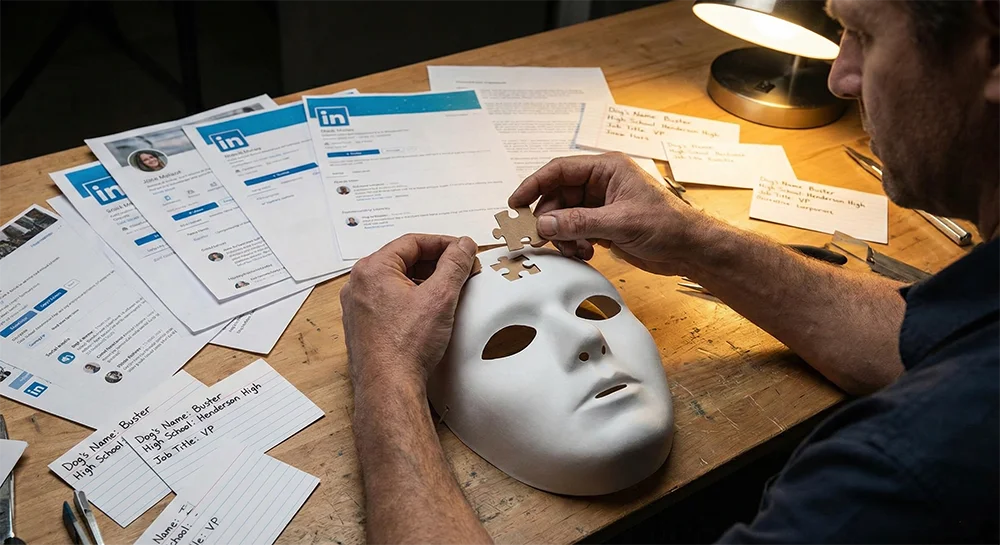
Unlike traditional breaches involving zero-day exploits or advanced malware, the MGM intrusion reportedly began with open-source intelligence (OSINT) and a convincing phone call.
Here’s how the attack unfolded:
- Reconnaissance: The attackers gathered publicly available information about MGM employees, likely from LinkedIn and other online sources.
- Impersonation: Armed with personal details, they called MGM’s IT helpdesk, impersonating an employee.
- Helpdesk Manipulation: The attackers convinced the helpdesk to reset account credentials and/or modify authentication factors.
- Privilege Escalation & Lateral Movement: Once inside, they escalated privileges, moved laterally across the network and ultimately deployed ransomware.
What Was the Impact and Cost?
The operational disruption lasted for days. Guests were unable to use digital room keys, ATMs and slot machines were impacted, and staff were forced to revert to manual processes. The reputational damage was immediate and highly visible.
MGM later disclosed that the cyberattack resulted in an estimated $100 million in financial impact, primarily due to lost revenue and recovery costs.
Additional expenses related to cybersecurity consulting, legal services and system remediation further compounded the damage.
The MGM breach reinforces several critical lessons:
- The helpdesk is part of your attack surface: Identity verification processes must be hardened and treated as high-risk control points.
- OSINT enables targeted social engineering: Publicly available employee information can dramatically increase attacker credibility.
- MFA is not a silver bullet: If attackers can reset authentication factors through support channels, MFA protections can be bypassed.
- Zero trust must include human workflows: Technical controls are only as strong as the operational procedures behind them.
We can help you reduce the risks with social engineering, feel free to contact us.