The hacking group LAPSUS$ claims to have stolen 3GB of internal data from pharmaceutical giant AstraZeneca, including source code, employee records, cloud infrastructure configurations, and access credentials. The hackers posted sample data on underground forums and are attempting to sell the complete dataset to the highest bidder.
AstraZeneca has not confirmed the breach. Cybersecurity News reports that the company “has not commented on the incident and no official statement has been released as of March 20, 2026.” The claims remain unverified and Hackread notes that “attribution in cybercrime forums is unreliable.”
The 3GB Sample Data Contains Real Internal Structures
Security researchers who reviewed the sample files found employee names, GitHub usernames with “Owner” privileges and 2FA status information. The data includes a directory tree showing a root folder named AZU_EXFIL containing what appears to be a supply-chain portal repository called “als-sc-portal-internal.”
The samples reveal structured internal exports that would enable privilege escalation attacks if genuine. LAPSUS$ has provided the data in .tar.gz format alongside screenshots as proof of access, following their established pattern from previous high-profile breaches.
The attackers are using the encrypted messaging app Session to negotiate sales rather than publicly dumping the data, signaling a shift toward direct monetisation over public extortion.
LAPSUS$ Previously Targeted Tech Giants, Not Pharma
LAPSUS$ gained notoriety in 2022 for breaching Microsoft, Nvidia, Samsung and other technology companies through social engineering attacks. The group used a range of tactics including calling IT helpdesks, impersonating employees, SIM swapping, MFA fatigue attacks, and targeting third-party suppliers to gain unauthorised access.
Their targeting of AstraZeneca represents an apparent expansion beyond their usual technology sector focus. The pharmaceutical industry has become an increasingly attractive target for cybercriminals seeking to steal intellectual property, though LAPSUS$ has historically focused on notoriety rather than financial gain.
The timing is problematic regardless of verification as AstraZeneca has a documented history of credential management failures that exposed patient data.
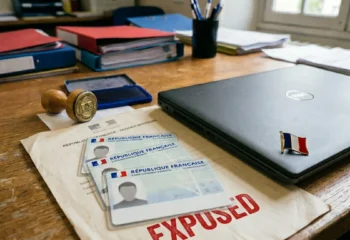
AstraZeneca’s Previous Security Failures
TechCrunch reported in November 2022 that AstraZeneca “blamed user error for leaving a list of credentials online for more than a year.” A developer had left login credentials on GitHub that granted access to a Salesforce test environment containing patient data from the AZ&ME discount programme.
The credentials were exposed publicly on GitHub in 2021 before being discovered by security researchers. AstraZeneca could not confirm whether anyone had accessed the data or what information might have been exfiltrated.
That incident demonstrates the same weakness LAPSUS$ typically exploits: poor credential hygiene and inadequate access controls that make social engineering attacks more effective.
References
- Hackread: LAPSUS$ Claims Alleged AstraZeneca Data Breach
- Cybersecurity News: AstraZeneca Data Breach – LAPSUS$ Group Claims Access
- TechCrunch: AstraZeneca Password Lapse Exposed Patient Data
- Cybersecurity lessons from the 2022 LAPSUS$ breaches
This post is also available in:

 March 23, 2026
March 23, 2026